November '17
Opinions, suggestions, recommendations or ideas found on our site are applied at your own risk. More.
The stupid neither forgive nor forget; the naive forgive and forget;
the wise forgive but do not forget. Thomas Szasz
And the old just don't care anymore :-D
PLEASE - Do not give control of your computer to ANYONE unless you
are absolutely certain who they
are!
For more information see our
Self Help > Scams!
In this newsletter
- Were you scammed? (101)
- But how did you get there in the first place?
- Did you allow control?
- Windows 10 Start menu
- More customization
- Shell commands
- Windstream billing
- Outlook printing
- Quickies

- CCleaner dangerous
- Experiment with Chrome
- Yahoo users a must read
- Symantec Endpoint renewal
Were you scammed? (101)
Not a redneck joke, but you know you were scammed if:
-
You allowed a support person (you do not know) to take over your computer and they showed you a bunch of problems on your computer.
-
Event logs, strange file names, "foreign" IP addresses and tons of cookies are all normal on a computer and do not indicate a problem. Discussed shortly.
-
-
They offered a multiyear (or even "lifetime") protection and support package.
-
They told you their server detected problems on your computer.
-
Unless your computer is part of a large corporate network, there is no server (anywhere) monitoring your personal computer. An exception to this may be a corporate level antivirus system such as Symantec's Endpoint protection (which we really like!), but even then, no one calls if something is detected, rather the account administrator simply receives an email notice.
See this example and why we like the product so much.
-
-
They mentioned anything about an IP address and/or seeing your computer, your network, your router or modem was compromised. See DNS hijacking.
-
You allowed them to take over and they showed you "services" running, not running or disabled.
-
Services have various states depending on the computer's current operation. Seeing some running, some not running and some disabled is completely normal! See services.
-
-
They were from Windows, Microsoft, Norton, McAfee or any other popular computer related company or term.
-
"Windows" is not a company and (again) none of the others monitor your computer, let alone call you when there are problems with it.
-
-
Finally and of course, they wanted money! Sometimes a lot of money.
-
They will not take a credit card, instead they want your checking/savings information or a debit card.
-
Been scammed? Report it to the FBI: https://www.ic3.gov/default.aspx
|
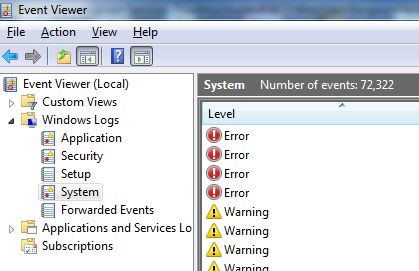
The System log tracks a lot of things that occur with the computer. Many are simply "informational" and generated by Windows itself. Over the past many years, we have never emptied our logs. We simply don't care or have time to bother with it. All event logs have a maximum size and after that, older log entries are replaced with newer entries, but anyway... Here is part of ours showing errors and warnings. We know the errors were from power supply issues and the warnings occurred as we reconfigured our (new) office network. No hacker here... |
 |
|
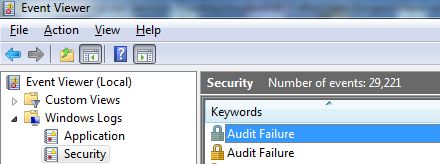
The Security log is most any action involving the operating system in general such as updates, installs, etc. Again even actions Windows itself takes are logged. In this example, it was not a hacker or virus, rather the Windows firewall was basically complaining it couldn't do something because our Symantec was in charge of firewalling our computer. |
 |
There is a large variety of event logs, but don't bother looking through them unless you are having a specific issue and you know what you are looking for.
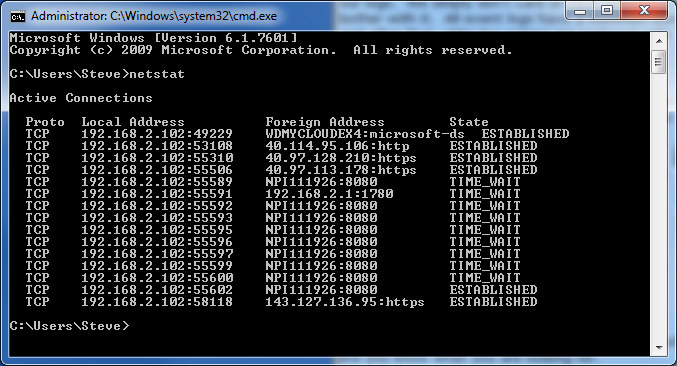
All computers connected to a network will show "foreign" addresses. These are simply connections to other devices, Windows itself, your antivirus application, etc., and are meaningless. They are not connections to other countries as the scammer will imply!
Strange file names
On one of the calls we received, the scammer told us to write
down 4 hackers' names and their "code names." We played
along.
Then he had us type this in the
Windows run box:
inf on hacker names
|
Knowing full well what inf does, we told him we typed info on hacker names then hit enter and nothing happened. We did this a couple times just to hear the frustration in his voice and eventually he became a bit irate. We asked why it wasn't working and if he could help us; he hung up. His end game would have been to show us a bunch of the hackers' "code
names" (those oddly named files) thereby proving our computer was infected. inf in the run box simply opens the legitimate Windows inf folder. Typing anything after inf is ignored by Windows. |
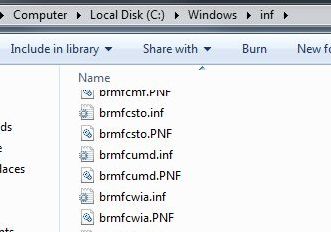 |
The inf folder is, as it (almost) sounds, a bunch of strangely named files with information about Windows, hardware, software, etc., but it is also a folder you need to stay out of. So forget this entire conversation :-)
Cookies
There are tons of them and as long as you have a good, active antivirus, forget all about cookies as well.
But how did you get there in the first place?
- Random phone call(s) typically with a obfuscated caller ID.
- We get many of these calls (it kind of brightens our day when we can play mind games with these scammers). Caller ID has shown an actual person's name, 800 numbers, ID containing the word service or support, unidentified caller and even our DSL provider's company name once.
- Just hang up!
- You receive an email message.
- If the email doesn't sound right, doesn't look legitimate or the sender's return address isn't legitimate (more information), simply delete the email!
- You are having problems with your computer, you do an
Internet search for technical support, you find a link to what you
believe is the manufacturer then call them.
- See our Who can you trust? page on how to determine if the search result is legitimate or not.
- See our list of manufacturer links.
If an online scam occurs taking over your computer, don't click anything, rather restart the computer then scan with your antivirus application and PowerEraser.
- An onscreen message indicates Java,
Flashplayer or
most anything else needs to be updated
before you can proceed.
- You don't need to click anything to get a message. Mostly these come from rogue advertisements on completely legitimate sites (that do not inspect/test ads before accepting them).
- The warning page may come up automatically because an ad is on a timer or your mouse happens to hover over or run across the ad. (Worst of all, they can be hidden ads.)
- See updates
- *** Recent virus ***
It spreads via a fake Flash update on compromised websites. And It can spread laterally across networks... ZDNet article.
- An onscreen message pops up or takes over your screen with
some dire warning and a phone number to call.
- Occurs for same reasons just stated.
- Your computer starts talking to you warning about a virus or other problem,
and reads off a phone number to call.
- Occurs for same reasons previously stated.
Again, just shut down, restart and scan!
Did you allow control?
If you allowed remote control, then refused to pay and see something like these, you are in trouble!
They encrypted your computer and there may or may not be a fix. More times than not on encrypted machines, we had to capture data and reinstall Windows (and everything else) from scratch.
 |
 |
Report scams:
-
Help Microsoft stop cybercriminals by reporting information about your tech support scam.
-
And/or the FTC Complaint Assistant form.
Windows 10 Start menu
|
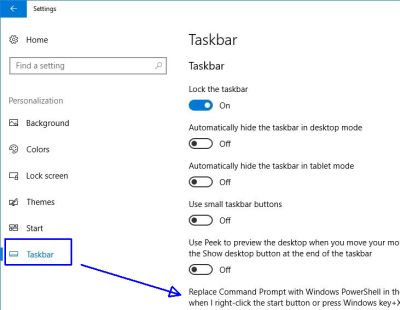
After a recent (and massive) update, you may find the Start menu's context menu changed. Two noticeable changes are:
The missing Control Panel almost seems to be a prelude to that application going away altogether and there is no quick key to get there either. For the Control Panel, you can type "control" in Cortana's search box or press Windows key + Pause/Break key then upper left, click Control Panel*. The Windows PowerShell can be replaced with the Command Prompt menu item via: Settings > Personalization > Taskbar and there, turn off the Replace Command Prompt with PowerShell option. |
 |
 |
 |
PowerShell is extremely powerful but somewhat complex
compared to
Command line tools (DOS commands).
Perhaps PowerShell will someday replace the
Command line tools.
*Note:
Another way you can get to the Control Panel (and a few other things)
is to type the following line in the
Windows run line (Windows key + R)
%LOCALAPPDATA%\Microsoft\Windows\WinX\Group2
(Enter or click OK). Interestingly,
%LOCALAPPDATA%\Microsoft\Windows\WinX\ offers a few
"groups" and within are other app shortcuts.
And of course, once you see a shortcut, you could certainly right click and send to your Desktop or pin/copy to the Start menu.
Aside but somewhat related: Microsoft's list of all Windows quick keys.
After the update
See this ZDNet article on 7 things you really should do!
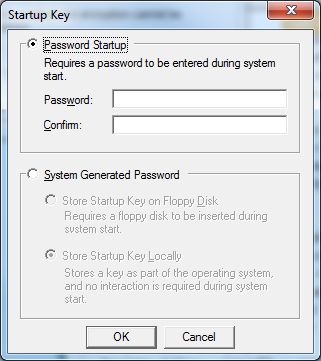
We agree with suggestion #1 and have posted that suggestion many times over the years. But likewise, we have also posted the dangers of doing suggestion #3. If you encrypt your drive and lose or forget the password, you're done!
More customization
Using Windows run line (Windows key + R), you can add items to the Start menu.
So for example: You installed an application but don't see an icon. What you will need to do is locate the application's program file (see our July newsletter) then copy and paste (or drag the shortcut) into one of these folders:
- C:\ProgramData\Microsoft\Windows\Start Menu\Programs
- Affects all users on the computer.
- C:\Users\<User>\AppData\Roaming\Microsoft\Windows\Start
Menu\Programs
- Affects only the currently logged-in users' list.
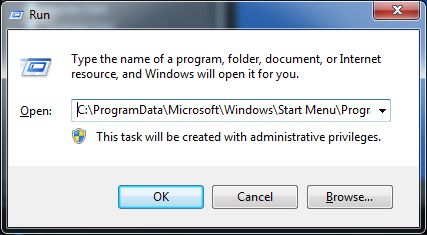
Note: C:\ProgramData is a hidden folder.
See Shell commands next.
Shell commands
If you want to open certain folders, you can do so using the Windows run line (Windows key + R).
shell:appdata opens the hidden Roaming folder where you can find all kinds of things to get in trouble with, but of interest would be the Microsoft > Windows > Start Menu > Programs folder as discussed above.
shell:Profile Displays the contents of
the current user profile in C:\Users\username.
shell:SendTo
Allows you to add or remove shortcuts on File Explorer's right-click
Send To context menu.
shell:Recent Displays a folder containing shortcuts
that appear in jump lists in Office apps, Explorer, and elsewhere.
These are as stated but probably just easier to access via their proper icon/shortcut:
shell:Desktop
shell:Downloads
shell:Personal
(your default
Documents folder)
shell:RecycleBinFolder
Windows creates "Public folders" which can be accessed by all users on the computer:
shell:Public
shell:Common Desktop
shell:Common Documents
shell:CommonPictures
shell:CommonMusic
shell:CommonVideo
shell:CommonDownloads
There are a lot more shell: commands; see this article.
Windstream billing
We had to contact Windstream to move our phone and DSL service, and as many of you may already know, calling their customer support can be challenging at best. Long story short, after literally hours (mostly on hold), we finally got our service moved (albeit 3 days later than initially agreed upon).
But they had failed to increase the speed as requested. So another call to get that fixed and we are up and running but the heart of the story:
As we were wrapping up that last call with them, we asked what the price increase would be and they said "with the DSL speed increase and Internet Security..." at which point we stopped them and asked what security? They were going to automatically, and without our permission, add a McAfee subscription to our bill (and at a price of over $100 a year).
So look over your phone bills carefully. You may very well be paying for things not needed, not used!
Outlook printing
If you use Outlook, you may have noticed printing of the calendar is not exactly friendly depending on the current view. For example, if you view monthly but want only today to print, you must change the view or File menu > Print then change options including the date range.
Fortunately Microsoft offers a Calendar Printing Assistant. While it's labeled for Outlook 2007, it works just fine with our Outlook 2013. Later versions are unknown.
Download and install the utility then open it from the Start menu (it did not create a Desktop shortcut).
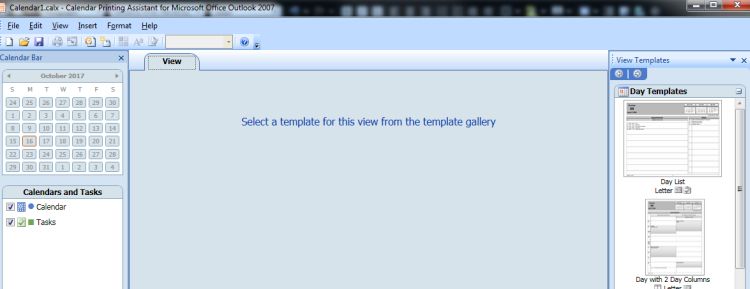
From the right panel, select a template, modify as desired then save the "project" to your Desktop or another handy location. When you want to print the calendar, simply open that project and print.
Quickies
Have Avast's CCleaner? It very well may have a hacker's backdoor allowing ransomware or keyloggers. The article and here is the FTC's response and article.
Have Google Chrome and like to experiment? Try typing this in
Chrome's addressbar:
chrome://flags/ (then press Enter)
But
heed the warnings :-)
Other Chrome commands - (have fun but be careful):
- chrome://dns
- chrome://downloads
- chrome://extensions
- chrome://bookmarks
- chrome://history
- chrome://memory
- chrome://net-internals
- chrome://quota-internals
- chrome://sync-internals
Yahoo user? READ THIS!
If you have Symantec Endpoint Corporate antivirus/protection, you may recall in the past it was necessary to call them if your credit card number changed. You can now log in to your account and change online:
Login into hostedendpoint.spn.com
Go to subscription
Click
on Buy More
Open the customer service TAB and select "Payment
Information"
Update your credit card details and save it.
Leaving you with
|
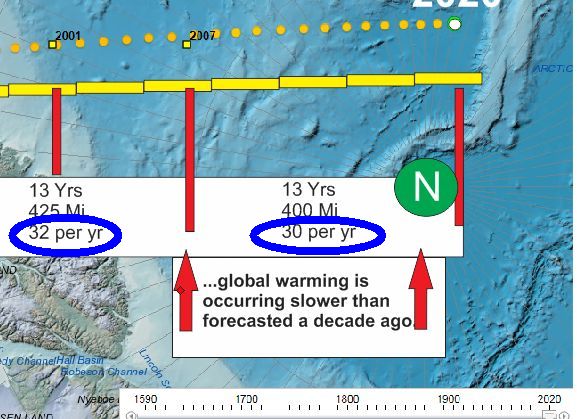
Remember our map (July '17) showing magnetic movement? According to this article "global warming" is slower than predicted just 10 years ago. Interestingly, the magnetic north movement also slowed over the past couple decades. Just pointing it out... |
 |
AND - Translator anyone?

Remember...
Thanks for all the help over these years, Jeff...